Secure messaging with a hacked phone
When facing the risk of your phone being compromised, due to travel or other factors, a bit of preparation can enable you to communicate securely, even if your phone is hacked.For context, it is worth reading general advice and a bit about business travel risks.
This process assumes you have completed the VIP Pre-Travel Checklist. The process can also be adapted to work with other devices such as tablets, laptops, or public workstations.
Requirements
You will need:− an Offline Device with requisite apps installed,
− a trusted counter-party, ideally with their own Offline Device,
− a passphrase that is shared with the counter-party, ideally not over a network.
This is outlined in the VIP Pre-Travel Checklist.
Overview
The high-level summary is that message composition and encryption is accomplished on the senders Offline Device, while the untrusted phone (or other end-point device) is simply used to transmit the encrypted payload.The receiver will decrypt and read the message on their Offline Device, thus keeping the plain-text and keys away from any untrusted system.
Sending Messages
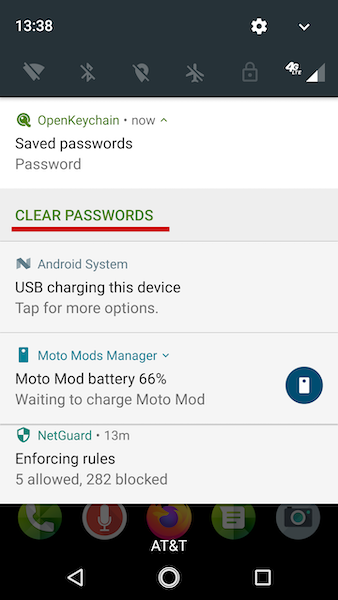
The process starts with the Offline Device:1. Launch the OpenKeychain App
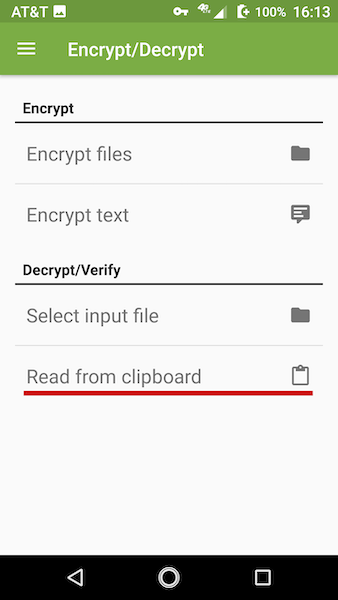
Then open the "Encrypt/Decrypt" section from the menu (highlighted in red below).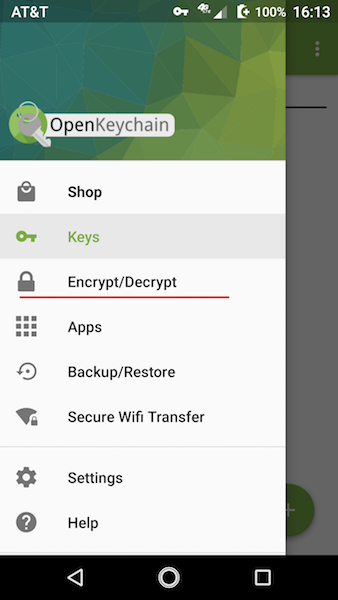
2. Select Encrypt Text
(highlighted in red below)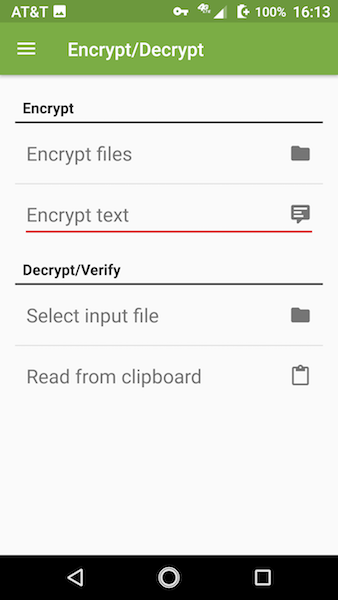
3. Open Options Menu
Click on the three vertical dots.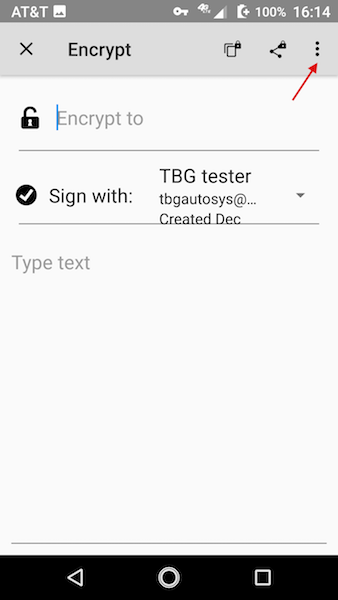
4. Check "Encrypt with password"
Then enter the shared passphrase for the counter-party (twice to confirm).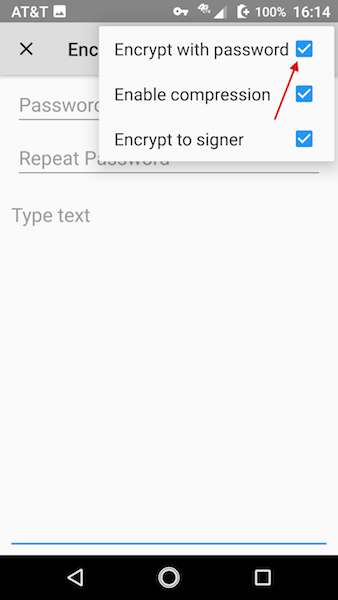
5. Compose message
Then click on either the "copy" icon or the "share" icon, depending on which app you are using for QR encoding. Our app automatically reads from the clipboard, others may vary.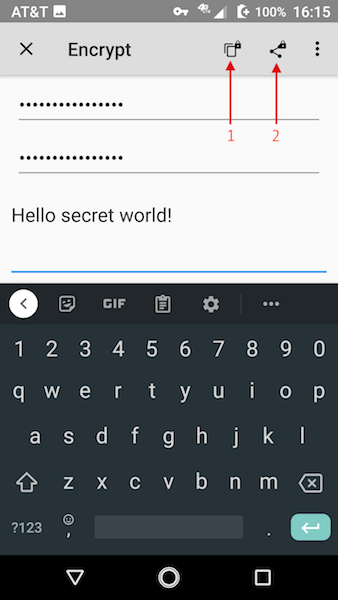
6. Display Encrypted Message as QR
You can then scan this message with an untrusted phone, tablet, or laptop and send the encrypted message using app or network of your choice (email, SMS, Facebook, etc.).
An alternate path is to use the secure USB drive to transfer the message (or other files that you've encrypted). After writing the encrypted file to the USB drive, be sure to enable the hardware write-protect switch before inserting it into an untrusted device (such as a PC in the hotel business center or internet cafe).
Receiving Messages
The process starts with the untrusted device:A. Display the Encrypted Message as QR
On the untrusted device if encrypted text was sent, rather than an image containing a QR code, you will need to render and display the message as a QR code. You can use any app or internet service for this, including our app (limited and ugly, but secure and open source).
B. Scan the QR with Offline Device
Most Android cameras have built-in QR decoding. Hover over the image with the Camera app, and then copy the QR text to the clipboard.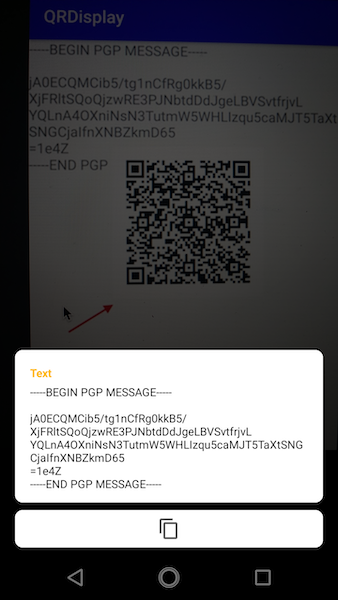
C. Launch the OpenKeychain App
Then open the "Encrypt/Decrypt" section from the menu (highlighted in red below).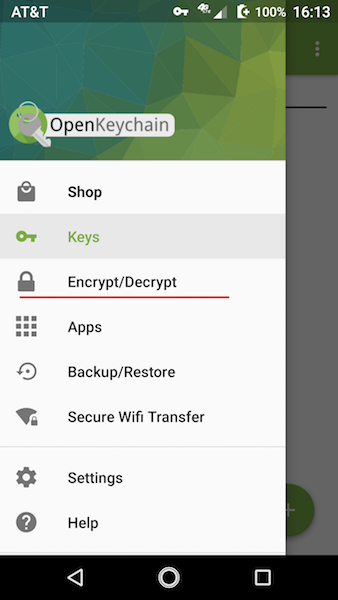
D. Select "Read from clipboard"
E. Enter the Shared Passphrase
You can then read the message on the Offline Device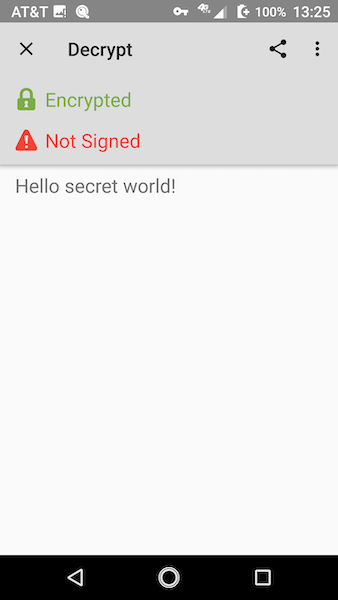
F. Clear the Passphrase!
When done reading the message, clear the passphrase form the Offline Device